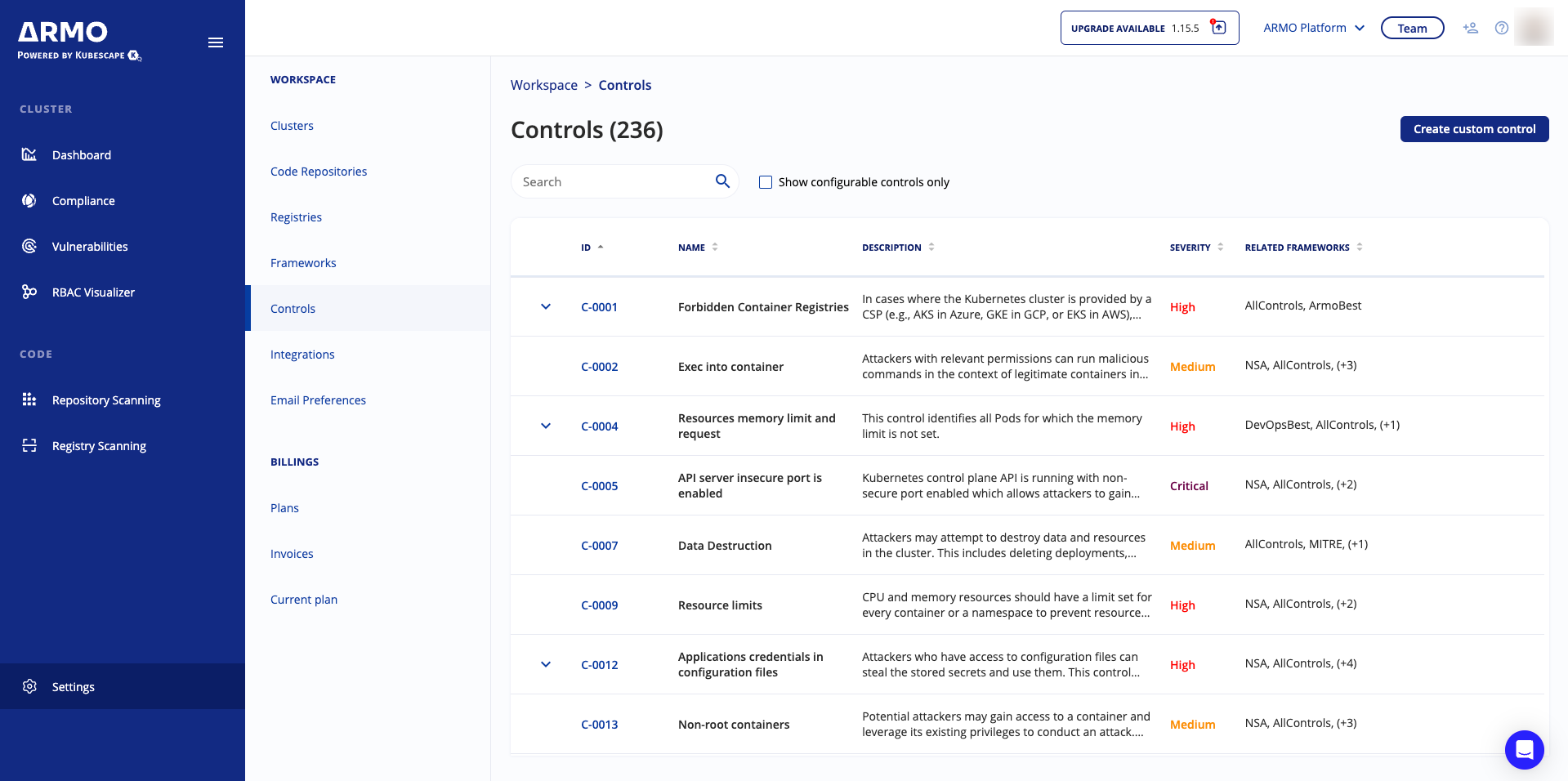
Controls
Security researchers and professionals codify best practices in controls: preventive, detective, or corrective measures that can be taken to avoid, or contain, a security breach.
ARMO provides hundreds of controls that can be used in either provided or custom frameworks. The controls are tests that look at a certain aspect of your security posture. We can examine:
- Kubernetes object configuration – any YAML file, any Helm chart, or any resource that the API server exposes.
- API server settings – configuration of the Kubernetes API server.
- Worker nodes – the configuration of the Kubernetes worker nodes, including kubelet configuration and host settings.
- Container images – the results from image scanning, to give you high-level visibility into items that need your attention.
ARMO Platform includes controls that are drawn from RegoLibrary, an open source library maintained by ARMO.
View controls
-
In the sidebar, click Settings.
-
Navigate to Posture, and click Controls.
Updated 7 months ago
